Shift of U.S. DoD Cybersecurity Standards – From DFARS and SP 800-171 to DFARS and CMMC
I traveled to the United States after a long time. This time, I visited AIA (Aerospace Industries Association), a trade association of the American aerospace and defense industry, and discussed the situation regarding standards application such as NIST SP 800-171. In short, I couldn’t help but felt the big change of direction from NIST SP 800-171 to CMMC (Cybersecurity Maturity Model Certification).
DoD started imposing its suppliers who access CUI the implementation of DFARS 252.204-7012 and NIST SP 800-171 in 2018, however a remarkable progress in the implementation hasn’t be announced so far. While we have been explaining the situation in the United States to companies in Japan, we were concerned how widespread the implementation actually is. Then, the U.S. DoD finally announced last year (in 2019) that CMMC framework shall be applied which encompasses requirements for contracts dealing with not only CUI but also all the other unclassified information. DoD is now drawing up a set of rules with version 0.7 released in December 2019 and planning to announce the initial implementation with version 1.0 by January 2020.
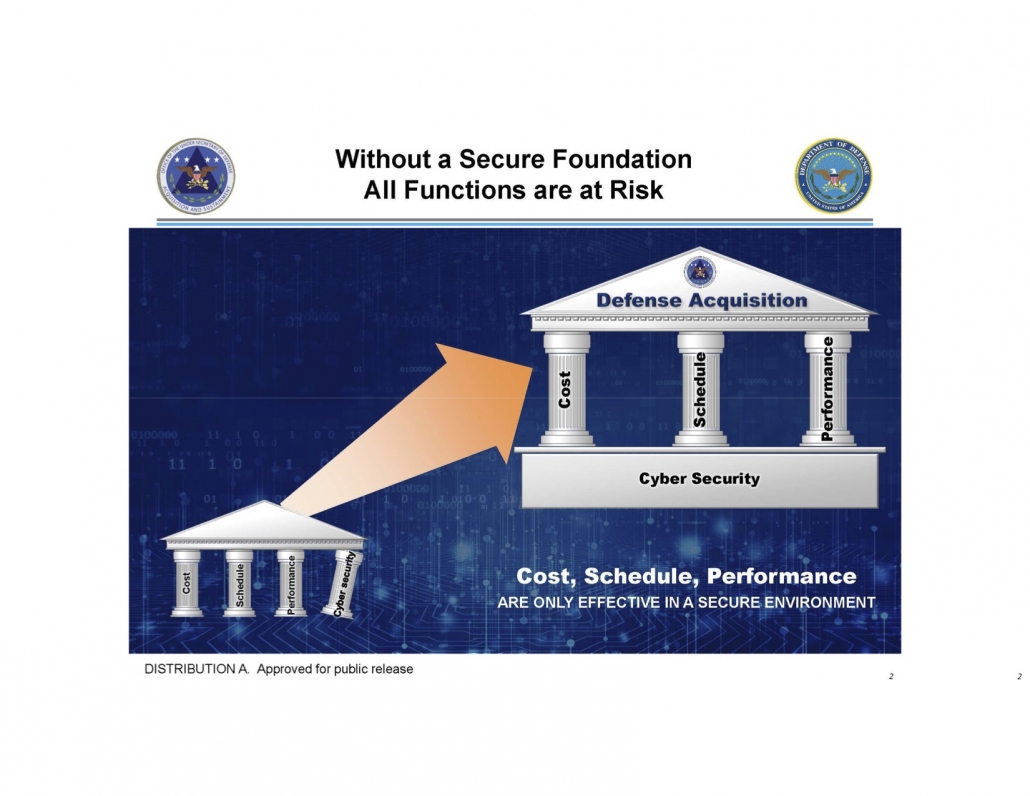
As the above figure emphasizes, “cyber security” is essentially a foundation rather than the fourth column equivalent to others such as “cost”, “schedule” and “performance”.
But why don’t DFARS and SP 800-171 work? One of the reasons is that when some of the 110 requirements cannot be satisfied, it made it acceptable if companies create a Plan of Action of Milestones (POA&M). Another reason is that the compliance was unpractical since the requirements weren’t a risk-based approach and were imposed uniformly on an entire supply chain.
CMMC was designed as an alternative approach to this. CMMC basically groups requirements into 5 levels. Organizations that wish to directly/indirectly contract with DoD must be certified at a minimum of Level 1. The required level of certification will depend on the access to information and/or threats and levels are dynamically simulated as needed. CMMC differs from conventional approach which uniformly requires every company having access to CUI to comply with all SP 800-171 requirements (equivalent to CMMC Level 3).
Then, what will happen to NIST SP800-171? SP800-171 is a set of security requirements defined by NIST, common across U.S. federal government which doesn’t depend on DoD policy. SP800-171 is revised to new editions year by year with 171A and 171B prepared, making practical tools available. Compliance to SP800-171 is still required for contracts with DoD and it’s expected other federal government agencies will continue the implementation, however; once CMMC is adopted in the defense industry in the near future, it can be anticipated that other federal agencies will follow the move.
How should Japanese defense industry be prepared? To begin with, achieving certification at Level 1 by fall 2020 in which CMMC becomes mandatory (DFARS revision) is important. Like DFARS, CMMC will also be required at the time of contract renewals and new contracts after fall 2020. Level 1 has the minimum requirements of 17 and it’s believed that achieving the certification at this level is possible in half a day. It shouldn’t be much of a problem for most of the Tier 1 companies.
That being said, since the flow-down clauses are still binding, it’s crucial to keep an eye on the action of DoD to make sure what kind of compliance is instructed for your own company and what kind of directions should be given to sub-suppliers.